Insider Threat Detection & Protection
One Platform. Three Layers of Security. Prevent, Detect, React
Prevent • Detect • Respond
Monitor All Devices from One Interface
A System of Insight
KNOW WHAT YOUR INSIDERS ARE DOING
- Record all user activity on the endpoint – even while not connected to the network
- Analyzes and indexes data for searches, alerts, audit trials, and benchmarking
- Replay key sessions and episodes to see the exact context of any situation
- Creates benchmarks of acceptable activities and alerts admins on variations

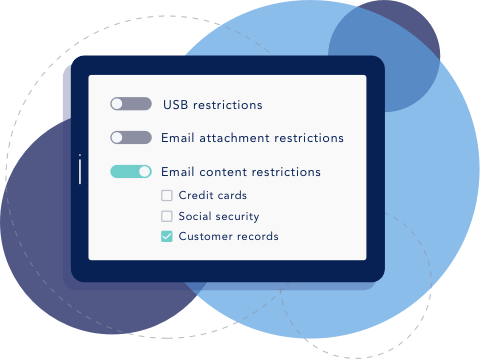
A System of Control
PROACTIVELY PREVENT HIGH-RISK ACCESS AND EXFILTRATION
- Set and enforce granular access policies
- Set and enforce granular exfiltration policies—including blocking data-in-motion (block emails or USBs)
- Set time-based controls to permit access to certain applications or programs during specific times
A System of Action
REACT FASTER AND MORE INTELLIGENTLY
- Remotely delete or retrieve files from any endpoint
- Lockdown an endpoint
- Follow up investigations
- Allow for case-by-case manual override of restricted activities

What makes InterGuard Insider Threat Detection Different?
Works On and Off Network
Deployed at the endpoint, InterGuard detects insider threats whether your employees are in the office or working remotely.
- No network required
- Ideal for today's mobile workforce

Our Cloud, Your Cloud or On-Prem
Our Cloud
The fastest and easiest way to get started. You don’t have to worry about buying hardware or a complicated setup. Just download your Cell Phone Monitoring licenses and get to work.
Your Cloud
Want to host your own cell phone monitoring software on-prem or on your private cloud? As long as you have SQL Server (Standard or Enterprise) and an existing Windows Server (2012, 2014, 2016 or 2017) then we will provide you with an installer that creates a database instance for InterGuard. No need to buy any additional hardware.

How Does it Work?
License
Either purchase license(s) or sign up for our Free Trial to create your web-based account.
Download
Download the agents from your web-based account. Remote deployment available for 10 licenses or more.
Monitor
Access your web-based InterGuard console which provides you with centralized reporting, policy control and comprehensive management.