Real-Time File Activity Monitoring
Protect Your Most Sensitive Files from Employee Misuse
Track File Activity and Prevent Insider Data Leaks
You can easily monitor and track all file activity events carried out by your employees, such as copying, deleting, editing, uploading, emailing and printing of your sensitive documents. InterGuard Employee Monitoring Software includes easy-to-understand insight into the activity, real-time alerts of suspicious access, and the ability to block access to select files and folders and from select users.
Automatic Monitoring
InterGuard's file activity tracking software monitors everything that happens on the employees endpoint, rather than being a network / file-based solution. This not only means you won't have to pre-define which files you want to monitor, but it also means files activity is continuously monitored even when the employee is not connected to your network.
Real-Time Alerts
Receive automatic email alerts triggered by pre-determined file activities (e.g. keyword, upload to Dropbox, higher than average print jobs). Review each flagged alert within the context of the user's activity session to determine if there's a threat.
Flexible Monitoring Policies
InterGuard makes it easy to set different file tracking policies according the the risk level of team, group or individual. For example, you may not want to be notified when your HR manager sends a file titled, "Salary List" to your accountant, but you certainly need to know if someone from the IT department is attempting to upload it to an external site or emailing it to a reporter.
Intuitive, Easy-to-Use Employee File Tracking Software
To start monitoring employee file activity with InterGuard's Employee Monitoring software, simply install the software on the employee's device and InterGuard immediately starts capturing data which you can access in real-time from our intuitive, web-based management interface.
Modified
Renamed
Deleted
Created / Downloaded
Attached to Email
Uploaded to USB
Uploaded to Cloud
Printed
InterGuard Makes File Tracking Easy.
Monitoring Employee File Activity Doesn't Have to Be Time-Consuming.
Increased mobility and remote working trends can make protecting sensitive documents seem overwhelming. InterGuard Employee Monitoring software makes it easy for you quickly and intuitively understand what's happening in your organization by offering a number of different, intuitive views to interpret your data.
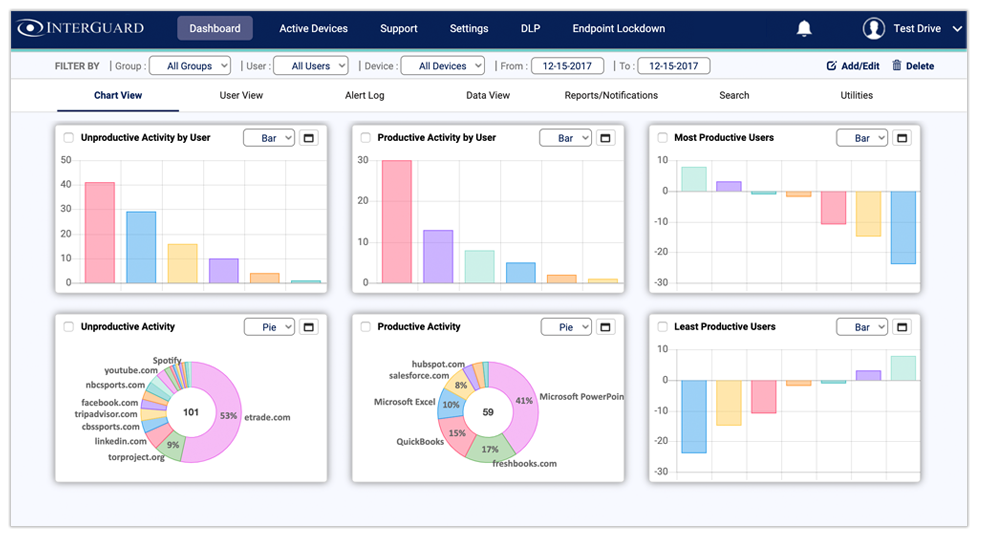
Bird's Eye View of All File Activity
Need a quick snapshot of your teams' file activity? The Chart View gives you interactive at-a-glance visual reports of everything that's happening with tracked files in your organization. For example:
- Users with Highest File Access Policy Violations
- Users with Highest Number of Print Jobs
Powerful Filtering Capabilities
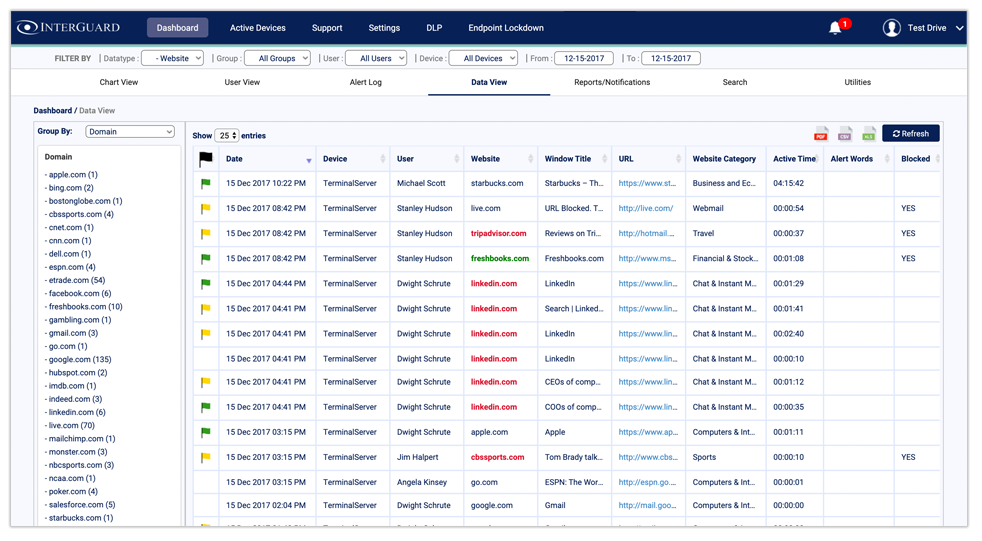
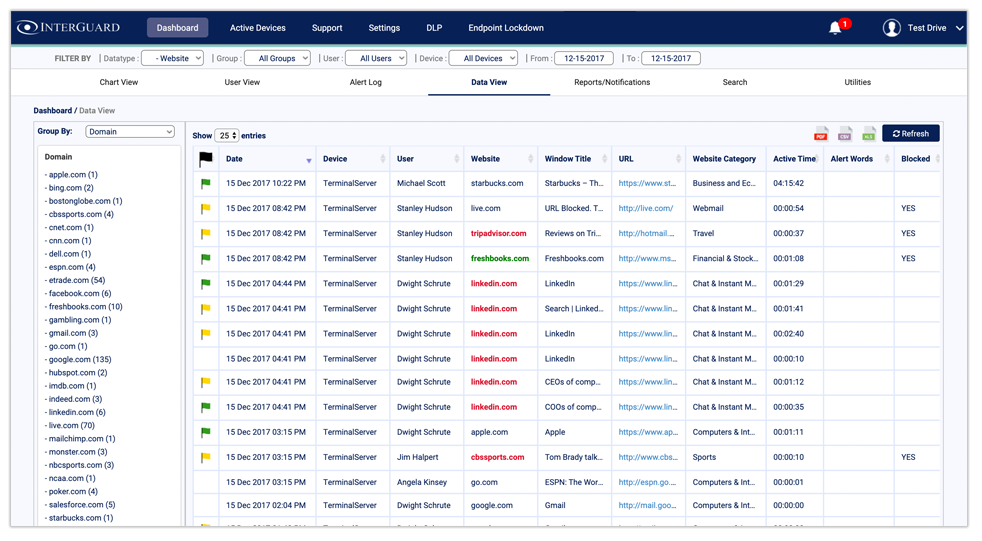
IInterGuard automatically tracks all employee file activity (e.g. prints, saves, uploads, etc) and presents it to you one data view that you can easily sort and filter in order to quickly understand what is going on. View all employee internet activity logs by date, device, user, website, window title, URL, website category, active time, alert word viewed on page, flag and search term.
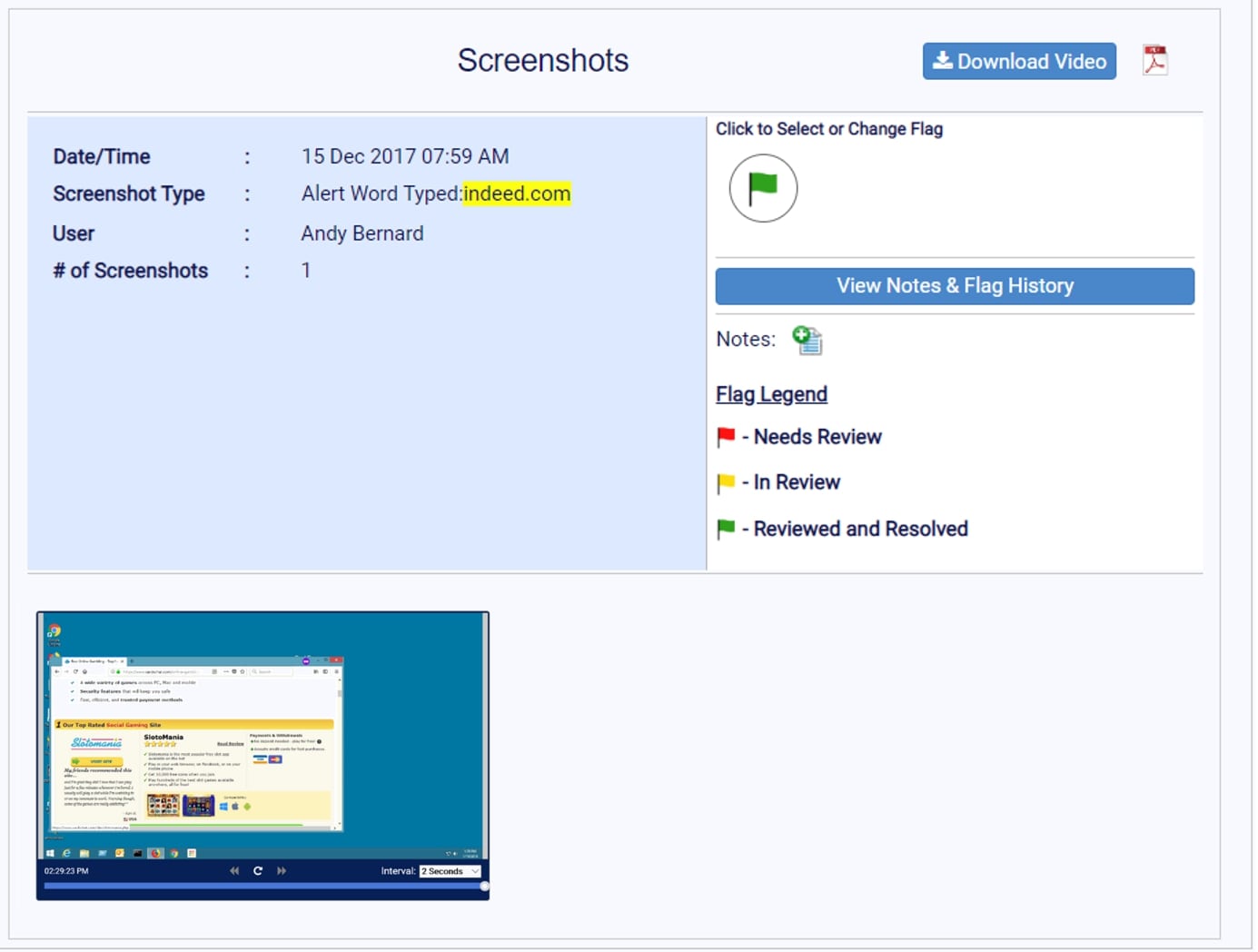
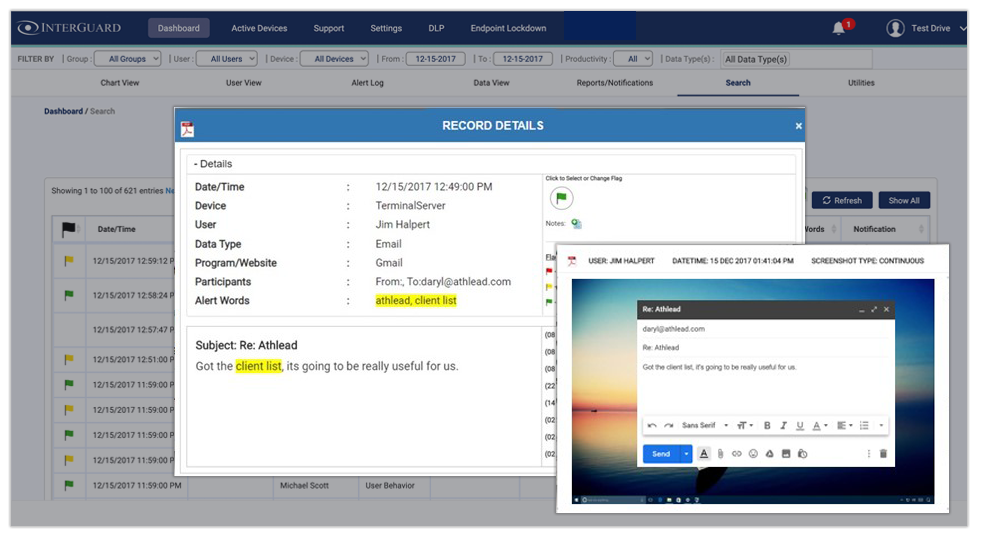
Suspicious File Activity Alerts with Screenshots
Trigger automatic screen capture every time a user views or types a specific keyword. Email notifications alert you each time a keyword is triggered, so you can quickly view the screenshot and investigation a potential data leak via file transfer. Consider keywords such as "client list", "product release", and "confidential".
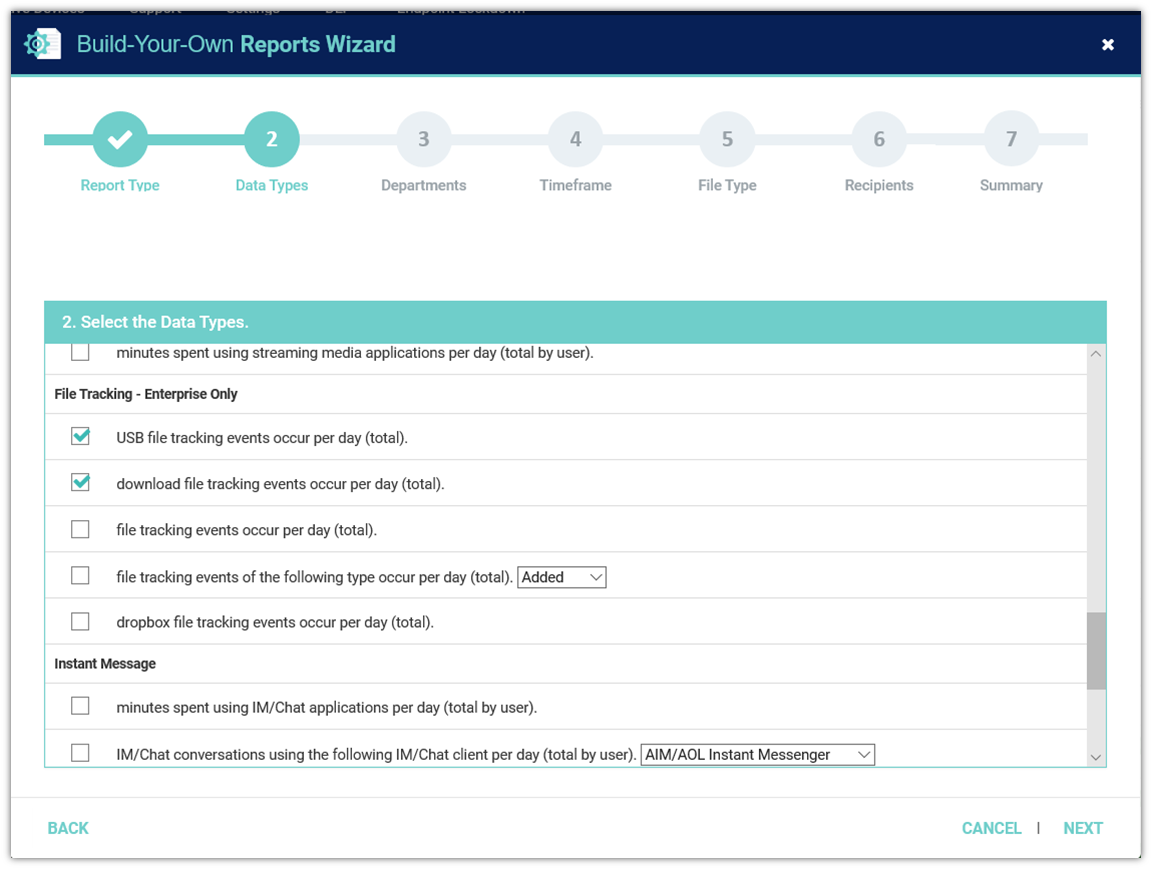
File Activity Reports
InterGuard's File Activity Report Wizard enables you to provide specified recipients with regular or ad-hoc email delivery of reports customized according to multiple criteria (e.g. file name, user, file action). Examples include:
- Webmail Attachments Sent by User
- Dropbox Uploads by User
- Deleted Files by By User Per Day
Powerful Search
InterGuard makes investigations faster and more accurate in the case of a suspected data leak or unauthorized access of sensitive files by malicious employees. Search by keyword to see all records of file activity either across your entire organization or by individual. Then filter results by user, time/date, device, flag, etc.
User Behavior Anomaly Detection
Deviation from routine file activity may indicate a potential problem. InterGuard will notify you about changes in individual, team or organizational file activity behavior and provide you with detailed contextual information so you can decide if the unusual activity is legitimate. We'll tell you what the norm is, and then you can choose to be notified either of behaviors that deviate by percentage or by absolute number above or below the norm.